In today’s fast-paced software development world, APIs (Application Programming Interfaces) play a crucial role in enabling communication between different applications. Whether you’re building a mobile app, a web application, or a service, APIs allow systems to exchange data securely. As the demand for seamless digital experiences grows, securing APIs becomes more important than ever.
One of the key aspects of API security is authentication — verifying the identity of a user or service before granting access to resources. In this blog post, I’ll walk you through two of the most common methods for securing APIs: OAuth and JWT (JSON Web Tokens). By the end, you’ll understand why authentication matters and how to decide which method suits your needs.
What is API Authentication?
API authentication ensures that only authorized users or systems can access an API. It helps verify that a request comes from a legitimate source and prevents unauthorized access to sensitive data. Authentication plays a crucial role in protecting your system from malicious users and potential data breaches.
When you implement API authentication, you focus on:
- Verification of identity: Ensuring the user or system trying to access the API is legitimate.
- Authorization: Checking whether the authenticated entity has the right permissions to access or perform specific actions.
- Access tokens: You exchange these secure tokens during authentication and use them to make authorized requests to the API.
OAuth: The Standard for Access Delegation
OAuth (Open Authorization) is an open standard that lets third-party services access a user’s resources without exposing their credentials (like username or password). OAuth provides a way to delegate access securely, allowing users to grant permission to a third-party application to act on their behalf.
How OAuth Works:
- Authorization Request: The user logs in and approves the requested permissions on the authentication server.
- Authorization Code: After the user grants permission, the server redirects them back to the client with an authorization code.
- Access Token: The client sends the authorization code to the server to obtain an access token.
- Access API: The client uses the token to make authorized requests to the API.
OAuth makes it possible to delegate access without sharing login credentials directly with third-party apps. This is especially useful when integrating with services like Google, Facebook, or GitHub, which lets users log in with existing accounts while keeping their login details private.
Key Features of OAuth:
- Token-Based Authentication: OAuth uses access tokens to authenticate API requests.
- Granular Access Control: OAuth lets users grant limited permissions to apps (for example, read-only access to a calendar or full access to contacts).
- Secure Delegation: OAuth tokens can be scoped, limited in lifespan, and revoked at any time, giving you better control over access.
When to Use OAuth:
- You need users to log in using third-party accounts like Google or Facebook.
- You want to manage access securely without sharing user credentials.
- You want to integrate your app with multiple third-party services.
JWT: A Compact, Self-Contained Authentication Token
JWT (JSON Web Token) is a compact and URL-safe method for transferring claims between two parties. A JWT is self-contained, meaning it holds all the information necessary for authentication and authorization, including user identity and permissions.
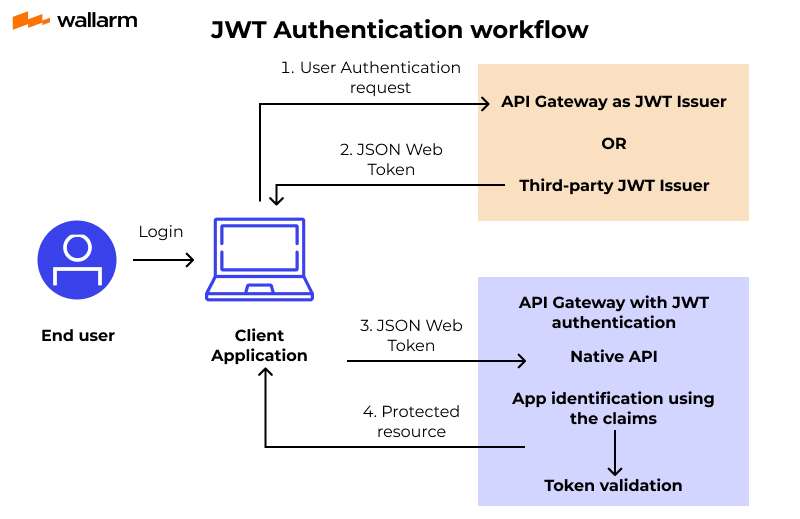
How JWT Works:
- User Login: After the user logs in, the server authenticates them and generates a JWT.
- Token Storage: The server sends the JWT to the client, and the client stores it in localStorage or cookies.
- API Request: For future API requests, the client includes the JWT in the Authorization header (typically as a Bearer token).
- Token Validation: The server validates the JWT’s signature to ensure it hasn’t been tampered with and that the user is authorized to access the requested resource.
Unlike OAuth, which involves several steps to acquire tokens, JWT is lightweight and easy to implement. You often use it for stateless authentication, where the server doesn’t need to store session data.
Key Features of JWT:
- Self-contained: JWTs store all the necessary information about the user and their permissions, so you don’t need extra database queries for authentication.
- Compact: JWTs are small in size, making them ideal for use in HTTP requests. You can pass them easily in URLs, headers, or cookies.
- Stateless: JWTs don’t require server-side session storage because all the information is embedded within the token itself.
- Flexible: The JWT payload can include any claim about the user, such as their roles, permissions, or token expiration time.
When to Use JWT:
- You need a stateless authentication system.
- You don’t require external user delegation to third-party services.
- You want a lightweight, self-contained token for API calls, without the need for server-side sessions.
OAuth vs. JWT: Key Differences
OAuth and JWT serve similar purposes — securing API access — but they differ in several ways.
OAuth is a better choice when you need to delegate access to external services, especially if your API interacts with third-party platforms (such as Google, Facebook, or other OAuth-compliant services). OAuth is more complex because it requires multiple steps for obtaining and refreshing tokens, but it provides a flexible and secure way to manage permissions.
On the other hand, JWT is perfect for simpler, stateless authentication systems. It is lightweight, self-contained, and easy to implement. You don’t need to store sessions on the server, and the token carries all the necessary information for authentication.
When to Choose OAuth or JWT?
- Choose OAuth when you need to allow users to grant access to their data without sharing login credentials or when your API interacts with multiple third-party services.
- Choose JWT when you need a lightweight, stateless authentication solution for your own system or application. JWT is ideal for securing API access based on user roles or claims without the need for third-party integrations.
Conclusion
API authentication is crucial for any modern web or mobile application. Both OAuth and JWT are powerful methods for securing API access, but they serve different purposes. OAuth works best for scenarios that require delegation of access, particularly when integrating with third-party services. JWT, on the other hand, is ideal for simple, stateless authentication in scenarios where you need a lightweight and self-contained token.